Last updated: 2026-04-30
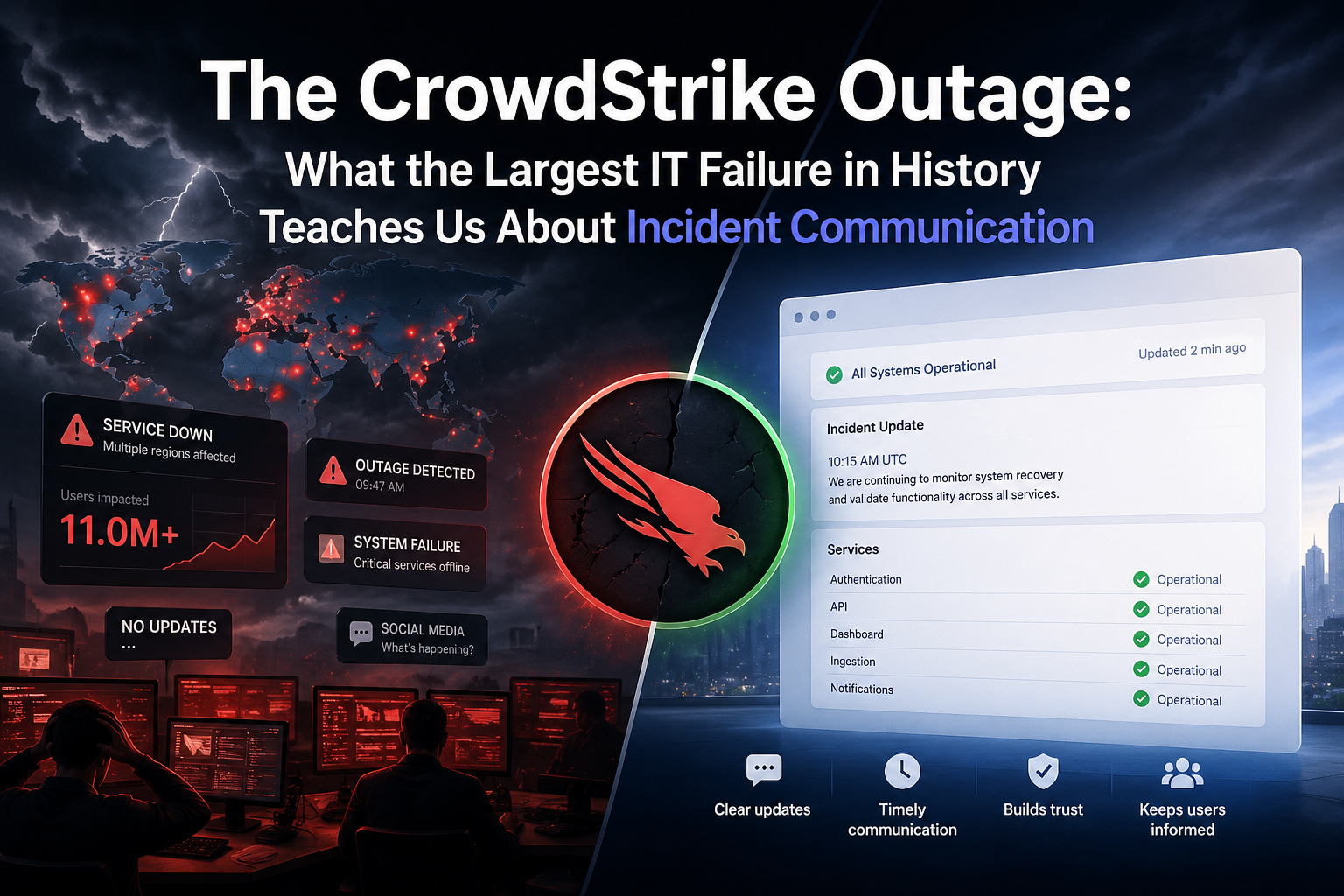
On July 19, 2024, at approximately 04:09 UTC, CrowdStrike pushed a routine sensor configuration update to its Falcon platform. Within minutes, an estimated 8.5 million Windows devices were showing blue screens of death simultaneously.
Airlines grounded fleets. Hospitals postponed surgeries. Banks locked customers out of accounts. Emergency services went offline in multiple countries. Delta Air Lines alone cancelled approximately 7,000 flights and reported losses exceeding $500 million. The economic damage, according to analysis by insurance firm Parametrix, exceeded $10 billion globally.
It was the largest IT outage in recorded history — not from a cyberattack, not from a state actor, but from a single faulty content update to a channel file.
And CrowdStrike’s status page was quiet for nearly an hour after the world started burning.
This is not a CrowdStrike hit piece. They handled some things well. But the incident offers a rare, specific, documented case study in what incident communication looks like at scale — and what it should never look like.
What actually happened (the timeline)
Understanding the communication failures requires understanding the timeline first.
| Time (UTC) | Event |
|---|---|
| ~04:09 | Channel file 291 deployed via automatic update to Falcon sensors |
| ~04:09–04:30 | BSOD reports flood Twitter/X, Reddit r/sysadmin, and IT forums globally |
| ~05:27 | CrowdStrike’s first public acknowledgment — a post on X by the company account |
| ~06:00 | Status page first updated (status.crowdstrike.com) |
| ~07:00 | First remediation workaround published (manual Safe Mode boot + file deletion) |
| ~12:00 | CEO George Kurtz posts formal apology on X |
| Days later | Detailed technical postmortem published on CrowdStrike blog |
The gap between 04:09 (incident start) and 06:00 (first status page update) is roughly 110 minutes. During that window, millions of IT administrators were diagnosing systems without any official acknowledgment of a known cause or a path to resolution.
That window is where trust was lost.
What CrowdStrike did right
Let’s be fair before being critical.
1. They identified the cause and named it clearly
Within hours, CrowdStrike publicly identified the specific cause: a logic error in channel file 291, not a cyberattack, not a breach. They did not hide behind vague “infrastructure issues” language. They named the component, explained the mechanism, and did not deflect blame onto Microsoft or end users.
This matters. Many vendors in similar situations issue statements like “some users may be experiencing issues” for hours before acknowledging a self-inflicted problem.
2. The CEO went public
George Kurtz posted a formal apology and explanation on X by midday. He personally stated: “CrowdStrike is actively working with customers impacted by a defect found in a single content update for Windows hosts.” He took ownership without hedging.
That kind of visible leadership during a crisis is rarer than it should be.
3. They published a detailed postmortem
Within days, CrowdStrike published a thorough technical postmortem explaining the content validator bug, the testing gap, and the deployment process that allowed a misconfigured file to reach production. It has been widely cited by the security and reliability engineering community as a model of transparency.
What CrowdStrike got badly wrong
1. A 110-minute status page silence while the world was on fire
The single largest communication failure was simply this: the world knew before CrowdStrike’s status page did.
By the time status.crowdstrike.com was updated, thousands of IT administrators had already identified the culprit via community forums and r/sysadmin, diagnosed their own systems, and were screaming for official guidance.
A status page that trails the community’s self-diagnosis by nearly two hours has already failed its primary purpose.
2. The first update stated a cause, not an impact
When CrowdStrike did update their status page, the initial framing was technical. It described the source of the issue — channel file 291 — without clearly stating the customer-facing impact: your Windows systems running Falcon are crashing on boot and will not recover automatically.
The right first update in any major outage follows a simple structure:
What is broken. Who is affected. What they cannot do right now. What we are doing. When we will update again.
Not: “We are aware of reports of crashes on Windows hosts related to the Falcon sensor.”
That sentence describes what is happening to CrowdStrike. It does not tell an IT administrator whether their entire Windows fleet is affected, whether cloud hosts are included, or whether there is anything they can do right now.
3. The manual remediation requirement was buried
This is the most operationally damaging failure.
The fix was not a patch. It was not a server-side rollback. It required a human to physically or remotely boot each affected machine into Windows Safe Mode, navigate to a specific directory, delete a specific file, and reboot.
At scale — across a hospital network, an airline’s gate systems, a bank’s ATM fleet — that means days of manual work. For systems that were BitLocker-encrypted (a large proportion of enterprise Windows environments), it required recovery keys from Azure AD, adding another layer of complexity.
This was not communicated clearly in the first hours. Engineers were attempting other workarounds and waiting for an automatic fix that was never coming. The manual remediation requirement should have been the headline of every update from the moment it was known.
The rule: if your users need to take action to recover, that is the most important thing you can tell them. Not the cause. Not the investigation status. The action.
4. Social media became the de facto status page
During the peak of the outage, the most reliable and detailed information was available not on status.crowdstrike.com, but on X, Reddit’s r/sysadmin, and tech news sites.
A company’s status page is supposed to be the authoritative source of incident information. When social media becomes more reliable than the official status page, the status page has already ceded its purpose.
This is a structural problem, not just a communication one. A status page that is only updated when someone on the response team finds a moment to open a dashboard will always lose to the crowd-sourced stream.
5. Scope was understated in early updates
CrowdStrike’s early updates used language like “some customers.” When your “some customers” is 8.5 million Windows devices spanning airlines, hospitals, and emergency services across multiple continents, that phrasing damages credibility for every subsequent update.
When affected customers read “some users” and their entire fleet is down, they stop trusting the status page entirely.
Eight things every engineering team should take from this
Most teams reading this do not run a cybersecurity platform worth tens of billions. But the lessons are not about scale. They are about discipline.
1. Your first update is not a diagnosis — it is an acknowledgment
The fastest possible public statement should say: We are aware of a problem. Here is what we know about who is affected. Next update at [time]. That is all. No cause required. No root analysis. Just: we know, here is the scope, here is when we will speak again.
2. “We are investigating” is not a status update
This phrase appears on status pages more often than almost any other text. It communicates nothing beyond “we have not fixed it yet.” Replace it with the current known scope, the action being taken, and the next update time.
3. If your fix requires user action, say that immediately
The moment your team determines that resolution requires action from customers — a restart, a manual step, a support ticket — that fact needs to be communicated before root cause analysis is complete. People cannot act on a cause. They can act on instructions.
4. Your status page must not share infrastructure with your product
Many SaaS status pages are hosted on the same servers as the application they report on. When those servers fail, the status page disappears exactly when users need it most. Run your status page on genuinely independent infrastructure. If the relationship between your product and your status page is “same provider, different region,” that is not sufficient. Correlated failures are real.
5. Estimate a timeline, even when you do not know
“We do not have a resolution ETA” is accurate. It is also the least useful thing you can say during an active outage. A better version: “We do not have a confirmed timeline. Based on current analysis, we expect more clarity within two hours. We will update at [specific time].” Specificity about uncertainty is more useful than vague honesty.
6. Do not let social media become your status page
If engineers at affected companies are getting better information from Reddit than from your official status page, you have a process problem. The solution is automation and process: monitoring that detects changes in state and triggers updates automatically, plus a team culture where updating the status page is the first action in any incident response process.
7. Communicate scope honestly, even when the number is frightening
An honest statement of “we believe this affects all Windows hosts running Falcon sensor version X with automatic content updates enabled” — even if the number is terrifying — is more useful than language about “some users.” Understating scope damages trust in everything that follows.
8. The postmortem is not a replacement for real-time communication
CrowdStrike’s postmortem was excellent. It arrived too late to help anyone manually booting 10,000 machines into Safe Mode on July 19th. A thorough postmortem does not retroactively fix communication that failed during the incident. Both matter independently.
The uncomfortable question this incident forces
CrowdStrike had resources almost no other company on earth can match: a dedicated security operations team, incident response playbooks, experienced communications staff, and years of experience managing security events.
Their status page was still quiet for nearly two hours while the world noticed.
That should make every engineering team ask an honest question: if it took a $10 billion cybersecurity company 110 minutes to update their status page, how long does it take us?
Most small teams do not have a status page process at all. Updates happen when someone finds time to open the dashboard. The customer communication comes after the fix. The post-incident message is “we’ve resolved the issue” with no context for what happened.
That is a default most teams accept without examining. It does not have to be.
A practical checklist for the next incident
When an incident starts, communication steps should run in parallel with the technical response — not sequentially after it.
| Step | Action | Timing |
|---|---|---|
| 1 | Post an acknowledgment — scope, not cause | Within 10 minutes of detection |
| 2 | Set the next update time in the first post | Same post |
| 3 | Communicate whether user action is required | As soon as known |
| 4 | Update at the committed time, even with no change | On schedule |
| 5 | State scope honestly — avoid “some users” if impact is broad | Every update |
| 6 | Publish resolution with a brief explanation | On resolution |
| 7 | Follow up with a postmortem or incident review | Within 5 business days |
The goal is not perfection under pressure. The goal is to ensure that customers have accurate, timely information at every stage — so they can make decisions, not just wait.
Related reading
- Why Your Status Page Is Useless During an Outage (And How to Fix It)
- Incident Communication Templates
- Incident Severity Levels Explained
- How to Set an Incident Update Cadence
FAQ
How many devices were affected by the CrowdStrike outage?
Microsoft confirmed approximately 8.5 million Windows devices were affected by the faulty CrowdStrike Falcon sensor update on July 19, 2024. This represents less than 1% of all Windows machines globally but was concentrated in enterprise and critical infrastructure environments.
What was the economic impact of the CrowdStrike outage?
Insurance and risk analysis firm Parametrix estimated the total economic impact at over $10 billion. Delta Air Lines alone reported losses exceeding $500 million and cancelled approximately 7,000 flights. The outage affected airlines, hospitals, banks, broadcast networks, and emergency services across multiple countries.
How long did it take CrowdStrike to update their status page?
Based on publicly available timelines, the first status page update at status.crowdstrike.com appeared approximately 110 minutes after the faulty update was deployed, despite widespread public reporting beginning within 20–30 minutes of the incident start.
Did the CrowdStrike outage require manual remediation?
Yes. The fix required booting each affected Windows machine into Safe Mode, navigating to C:\Windows\System32\drivers\CrowdStrike\, and deleting the file matching C-00000291*.sys. For BitLocker-encrypted devices, the process required an additional recovery key retrieval step from Azure AD. Automated recovery was not possible — every affected machine required individual human intervention.
What is the most important lesson from the CrowdStrike incident communication?
The most operationally significant failure was the delayed communication that the fix required manual intervention on every affected machine. Teams that knew this early could begin planning the recovery effort. Teams that waited for official guidance lost hours. The lesson: if resolution requires user action, communicate those instructions before root cause analysis is complete.